|
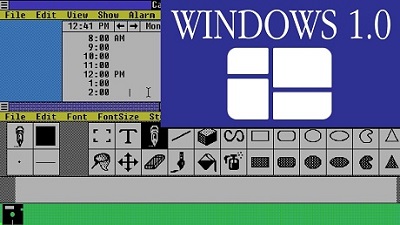
What do Cristiano Ronaldo, Bruno Mars, and Windows have in common? They're all 35 years old. It is three and a half decades since Microsoft Windows 1.0 was unleashed upon an unsuspecting world. Tottering atop MS-DOS, Windows 1.0 was released on 20 November 1985. A graphical multitasking shell, it would usher in an era of dominance on the PC that lingers on today. The secret sauce was IBM support, which brought a huge chunk of the business world along, for better or worse. Not that dominance was a sure thing back then. Windows 1.0 was by no means the only game in town: this hack has fond memories of GEM (Graphics Environment Manager) which turned up in computers from Amstrad to the Atari ST. At the time Windows was one among many, and it would take a good few iterations before the 3.x line began to dominate. First shown off two years previously, Windows 1.0 would run on 256KB of RAM and a pair of floppy drives (later versions would require a hard disk) and, most significantly, require the user to move a mouse-pointer to make things happen in the 16-bit shell. At least 512KB was needed before performance improved beyond dragging Notepad through treacle. Windows 1.0 also suffered from an initial paucity of apps, with the likes of Calculator and Paint coming in the box while many MS-DOS applications would fire up in full-screen mode. The GUI also insisted on tiling the windows - no overlapping was allowed other than dialogs. After a number of incremental improvements, Windows 1.0 was replaced by Windows 2.0 in 1987, although it lingered on until support for it (as well as versions 2.0 and 3.0) ended in 2001. Windows was the mainstay of Microsoft profits in the 90s, thanks to some sharp elbows on the OEM front from its legal department. The money rolled in, and Redmond wanted more. When smarter mobile phones started kicking off in the late 90s, Microsoft made its first of many failed attempted to break into the mobile market with Windows CE or WinCE as it became known. It didn't last long, despite some notable handsets, but Microsoft kept trying. Enthused by then-CEO Steve Ballmer, who had originally dismissed the iPhone, Microsoft tried again with Windows Phone 7, launched in 2010. Despite excellent hardware from Nokia, which Redmond bought and then gutted, the OS never caught on with developers, and a lack of backward compatibility with the new kit killed demand. As for tablets, Redmond first dipped Windows' toe into the market in 2003 with the Microsoft Tablet PC. Redmond has kept up its interest in this area - and the latest Surface fondle slabs are very nice, if expensive, pieces of kit. Now Windows has evolved into a cloud operating system and is maintaining its position in the mainstream. Microsoft has managed to make the transition from in-box code to cloud better than most, albeit a bit late. Ray Ozzie, hired as Microsoft's cloud guru in 2006, saw the writing on the wall and warned Redmond that Windows would have to get cloudy. He was forced out, although not before founding Azure, the smart folks took note - not least Satya Nadella, who is cloud to the core. It seems odd that senior Windows coders now weren't even a glint in the milkman's eye when the first build of the OS came into being. But the effect of the operating system is undeniable. Looking back, Windows 1.0 was a curiosity in spite of the enthusiasm for the product by Microsoft boss, Bill Gates. Business users were content to stick with DOS while consumers looked to alternatives, including the likes of Atari or Commodore, for their home computing fun. However, Windows 1.0 marked a change for Microsoft and an attempt to focus more on applications. APIs for video and mouse hardware moved things on from the DOS environment and PC software and hardware makers would flock to the platform as the decades rolled by. For better or for worse. Complete details are posted on OUR FORUM. Last Thursday afternoon, Mac users everywhere began complaining of a crippling slowdown when opening apps. The cause: online certificate checks Apple performs each time a user opens an app not downloaded from the App Store. The mass upgrade to Big Sur, it seems, caused the Apple servers responsible for these checks to slow to a crawl. Apple quickly fixed the slowdown, but concerns about paralyzed Macs were soon replaced by an even bigger worry—the vast amount of personal data Apple, and possibly others, can glean from Macs performing certificate checks each time a user opens an app that didn’t come from the App Store. For people who understood what was happening behind the scenes, there was little reason to view the certificate checks as a privacy grab. Just to be sure, though, Apple on Monday published a support article that should quell any lingering worries. More about that later—first, let’s back up and provide some background. Before Apple allows an app into the App Store, it must first pass a review that vets its security. Users can configure the macOS feature known as Gatekeeper to allow only these approved apps, or they can choose a setting that also allows the installation of third-party apps, as long as these apps are signed with a developer certificate issued by Apple. To make sure the certificate hasn’t been revoked, macOS uses OCSP—short for the industry-standard Online Certificate Status Protocol — to check its validity. Checking the validity of a certificate—any certificate—authenticating a website or piece of software sounds simple enough, but it has long presented problems industrywide that aren’t easy to solve. The initial means was the use of certificate revocation lists, but as the lists grew, their size prevented them from working effectively. CRL gave way to OCSP, which performed the check on remote servers. OCSP, it turned out, had its own drawbacks. Servers sometimes go down, and when they do, OCSP server outages have the potential to paralyze millions of people trying to do things like visit sites, install apps, and check email. To guard against this hazard, OCSP defaults to what’s called a “soft fail.” Rather than block the website or software that’s being checked, OCSP will act as if the certificate is valid in the event that the server doesn’t respond. Somehow, the mass number of people upgrading to Big Sur on Thursday seems to have caused the servers at ocsp.apple.com to become overloaded but not fall over completely. The server couldn’t provide the all-clear, but it also didn’t return an error that would trigger the soft fail. The result was huge numbers of Mac users left in limbo. Apple fixed the problem with the availability of ocsp.apple.com, presumably by adding more server capacity. Normally, that would have been the end of the issue, but it wasn’t. Soon, social media was awash in claims that the macOS app-vetting process was turning Apple into a Big Brother that was tracking the time and location whenever users open or reopen any app not downloaded from the App Store. The post Your Computer Isn’t Yours was one of the catalysts for the mass concern. It noted that the simple HTML get-requests performed by OCSP were unencrypted. That meant that not only was Apple able to build profiles based on our minute-by-minute Mac usage but so could ISPs or anyone else who could view traffic passing over the network. (To prevent falling into an infinite authentication loop, virtually all OCSP traffic is unencrypted, although responses are digitally signed.) Fortunately, fewer alarmist posts like this one provided a more helpful background. The hashes being transmitted weren’t unique to the app itself but rather the Apple-issued developer certificate. That still allowed people to infer when an app such as Tor, Signal, Firefox, or Thunderbird was being used, but it was still less granular than many people first assumed. In an attempt to further assure Mac users, Apple Monday published a post. It explains what the company does and doesn’t do with the information collected through Gatekeeper and a separate feature known as notarization, which checks the security even of non-App Store apps. The post went on to say that in the next year, Apple will provide a new protocol to check if developer certificates have been revoked, provide “strong protections against server failure,” and present a new OS setting for users who want to opt-out of all of this. The controversy over behavior that macOS has been doing since at least the Catalina version was introduced last October underscores the tradeoff that sometimes occurs between security and privacy. Gatekeeper is designed to make it easy for less experienced users to steer clear of apps that are known to be malicious. To make use of Gatekeeper, users have to spend a certain amount of information to Apple. Not that Apple is completely without fault. For one thing, developers haven’t provided an easy way to opt-out of OCSP checks. That has made blocking access to ocsp.apple.com the only way to do that, and for less experienced Mac users, that’s too hard.For more turn to OUR FORUM. European privacy activist noyb has filed a complaint to Data Protection Authorities in Germany and Spain against Apple due to its use of an opt-out tracking cookie on all iPhones. The issue is due to Apple’s tracking code “IDFA”. IDFA (Apple’s Identifier for Advertisers) allows Apple and all apps on the phone to track a user and combine information about online and mobile behavior. Just like for cookies, this would require the users’ consent under EU law. Apple places these tracking codes without the knowledge or agreement of the users. By default, iOS automatically generates a unique “IDFA” (short for Identifier for Advertisers) for each iPhone. IDFA allows Apple and other third parties to identify users across applications and even connect online and mobile behavior (“cross-device tracking”). Apple’s operating system creates the IDFA without the user’s knowledge or consent. After its creation, Apple and third parties (e.g. application providers and advertisers) can access the IDFA to track users’ behavior, elaborate consumption preferences, and provide personalized advertising. noyb says such tracking is strictly regulated by the EU “Cookie Law” (Article 5(3) of the e-Privacy Directive) and requires the users’ informed and unambiguous consent. “EU law protects our devices from external tracking. Tracking is only allowed if users explicitly consent to it. This very simple rule applies regardless of the tracking technology used. While Apple introduced functions in their browser to block cookies, it places similar codes in its phones, without any consent by the user. This is a clear breach of EU privacy laws.” – Stefano Rossetti, privacy lawyer at noyb.eu. The system is currently Opt-out, meaning users are automatically tracked. Recently Apple announced plans for future changes to the IDFA system to Opt-in. Just like when an app requests access to the camera or microphone, the plans foresee a new dialogue that asks the user if an app should be able to access the IDFA. These changes seem to restrict the use of the IDFA for third parties, but crucially not for Apple itself. The initial storage of the IDFA and Apple’s use of it will still be done without the users’ consent and therefore in breach of EU law. It is also unclear when and if these changes will restrict 3rd party developers will be implemented by the company. “We believe that Apple violated the law before, now and after these changes. With our complaints we want to enforce a simple principle: trackers are illegal unless a user freely consents. The IDFA should not only be restricted but permanently deleted. Smartphones are the most intimate device for most people and they must be tracker-free by default.” – Stefano Rossetti, a privacy lawyer at noyb.eu Google uses a similar tracking system, which is currently being reviewed by noyb. As the complaint is based on Article 5(3) of the e-Privacy Directive and not the GDPR, the Spanish and German authorities can directly fine Apple, without the need for cooperation among EU Data Protection Authorities as under GDPR. “These cases are based on the “old” cookie law and do not trigger the cooperation mechanism of the GDPR. In other words, we are trying to avoid endless procedures like the ones we are facing in Ireland,” said Stefano Rossetti, a privacy lawyer at noyb.euFor more visit OUR FORUM.
|
Latest Articles
|