|
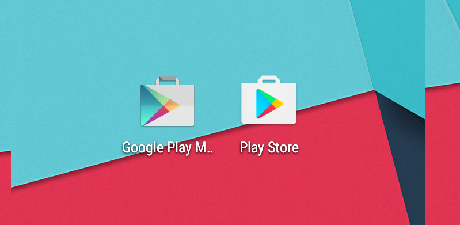
A malicious app called "Album by Google Photos" was found in the Microsoft Store today that pretends to be from Google. This app pretends to be part of Google Photos but is actually an ad clicker that repeatedly opens hidden advertisements in Windows 10. This free Album by Google Photos app claims to be created by Google LLC and has a description of "Finally, a photos app that's as smart as you.". You can see an image of its Microsoft Store page below. As this is an ad clicker, the reviews for the app are not very good. One review calls it a "Fake App" and another is titled "Fake, do not install". The Album by Google Photos app is a PWA app (progressive web app) that acts as a front end to Google Photos, but with a bundled ad clicker. While the app is running, this ad clicker will repeatedly connect to remote hosts and display advertisements in the background in order to generate revenue for the developers. The ad clicker component consists of three files located in the app's folder called Block Craft 3D.dll, Block Craft 3D.exe, and Block Craft 3D.xr. You can see these files in the image of the folder below. When a user starts the Album by Google Photos app they will be greeted by a screen asking them to log in to Google Photos. This is a legitimate login screen from Google and though I did not see any indications that your logins are being stolen, I would still not advise logging into Google Photos with this app. After the app reads the configuration file, it will connect to the various "AdBanner" URLs and display them in the background. You can see in the Fiddler traffic below the app connecting to each of the ad URLs. Navigate to OUR FORUM to learn more. No this is not a drill. The internet is going to shut down in less than 12 hours for a DNS encryption update by ICANN. However, you don’t need to panic as you won’t lose access to your precious cat videos. The Internet Corporation of Assigned Names and Numbers (ICANN) is planning to update the cryptographic key that helps protect the Domain Name System (DNS). For those who don’t know, DNS is like a directory which records all the domains and the owner of those domains. Seeing the ever-increasing security attacks and breaches ICANN decided to update the encryption keys for the DNS addresses. This means that when the update is taking place on a certain website, it won’t be accessible to the users. This also implies that the internet won’t be completely down as the update will happen in batches. The update has been scheduled strategically to happen over the weekend so it won’t disturb the day-to-day work of the organizations that rely on the internet. However, this also means that there’s a fair chance that you won’t be able to binge watch your favorite show on Netflix over the week. ICANN has already run several tests and has confirmed that only 1% of the world will experience issues but the number still comes to a little over 36 million users. That said if you’re one of the unlucky 1% of the users, then you don’t need to panic. The shutdown is temporary and requires no extra steps from the users. The best you can do is restart your modem or double check your DNS to make sure your DNS address is updated by your Internet Service Provider (ISP). For more detail visit OUR FORUM. A newly discovered piece of malware for Android raises the bar in terms of sophistication and flexibility, offering its operator adaptability to various tasks. Cybercriminals are currently running tests on GPlayed but malware analysts warn that it is already shaping up as a serious threat. The modular architecture extends its functionality through plugins that can be added without the need to recompile and update the package on the device. The operator can also inject scripts and send .NET code to the infected Android that GPlayed can compile and execute. it is built using the Xamarin environment for mobile apps and uses a DLL called "eCommon" that "contains support code and structures that are platform independent." This model shows a new step on the evolution ladder, where code can migrate from desktop platforms to mobile ones, resulting in a hybrid threat. It disguises itself on the device as the Play Store app, using an icon very similar to the original and the name "Google Play Marketplace." It asks for many permissions, including "BIND_DEVICE_ADMIN," which gives it almost complete control over the infected device. Researchers at Cisco Talos analyzed GPlayed and discovered a hefty set of native capabilities covering spying, data exfiltration, and self-management functions. Visit OUR FORUM for complete details. |
Latest Articles
|